Scattered Spider: $115M Ransomware Threat Exposed
Scattered Spider cybercrime group exposed in $115 million ransomware operation targeting major enterprises. Investigation reveals sophisticated social engineering tactics and persistence methods.
Expert analysis from Ricnology
Scattered Spider cybercrime group exposed in $115 million ransomware operation targeting major enterprises. Investigation reveals sophisticated social engineering tactics and persistence methods.

Nation-state actors compromise F5 BIG-IP source code in targeted breach. Technical analysis reveals attack vectors, exposure risks, and defensive measures organizations must implement to protect infrastructure.

Chinese threat group Jewelbug extends cyber espionage operations to Russian IT networks using sophisticated persistence mechanisms. Organizations must enhance threat detection and monitoring capabilities.
Scattered Spider's $115M ransomware operation exposes critical security strategy gaps in enterprise identity management, privileged access controls, and incident response planning that must be addressed.
Active exploitation of critical cookie vulnerability in ICTBroadcast servers enables authentication bypass and system compromise. Organizations running ICTBroadcast must apply patches immediately to prevent attacks.

Critical CVSS 10.0 vulnerabilities discovered in Red Lion RTUs threaten industrial control systems. Organizations must patch immediately to prevent remote takeover of critical infrastructure assets.
Federal investigation ties Scattered Spider cybercrime group to $115 million in ransomware extortion payments across enterprise victims. Analysis reveals advanced social engineering and identity compromise tactics.
WordPress sites targeted in widespread ClickFix phishing campaign exploiting vulnerable themes and plugins to inject malicious code that tricks users into executing PowerShell commands, compromising credentials and deploying malware

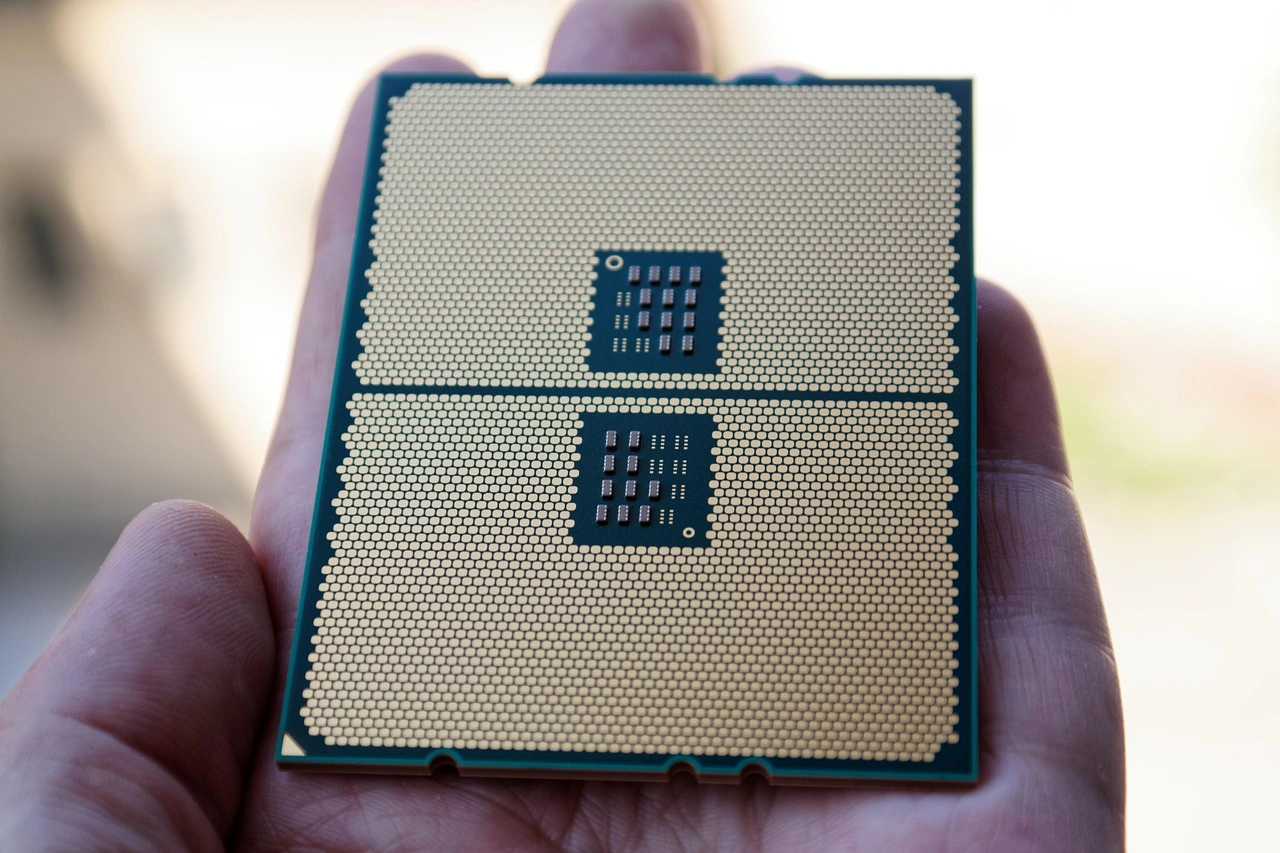
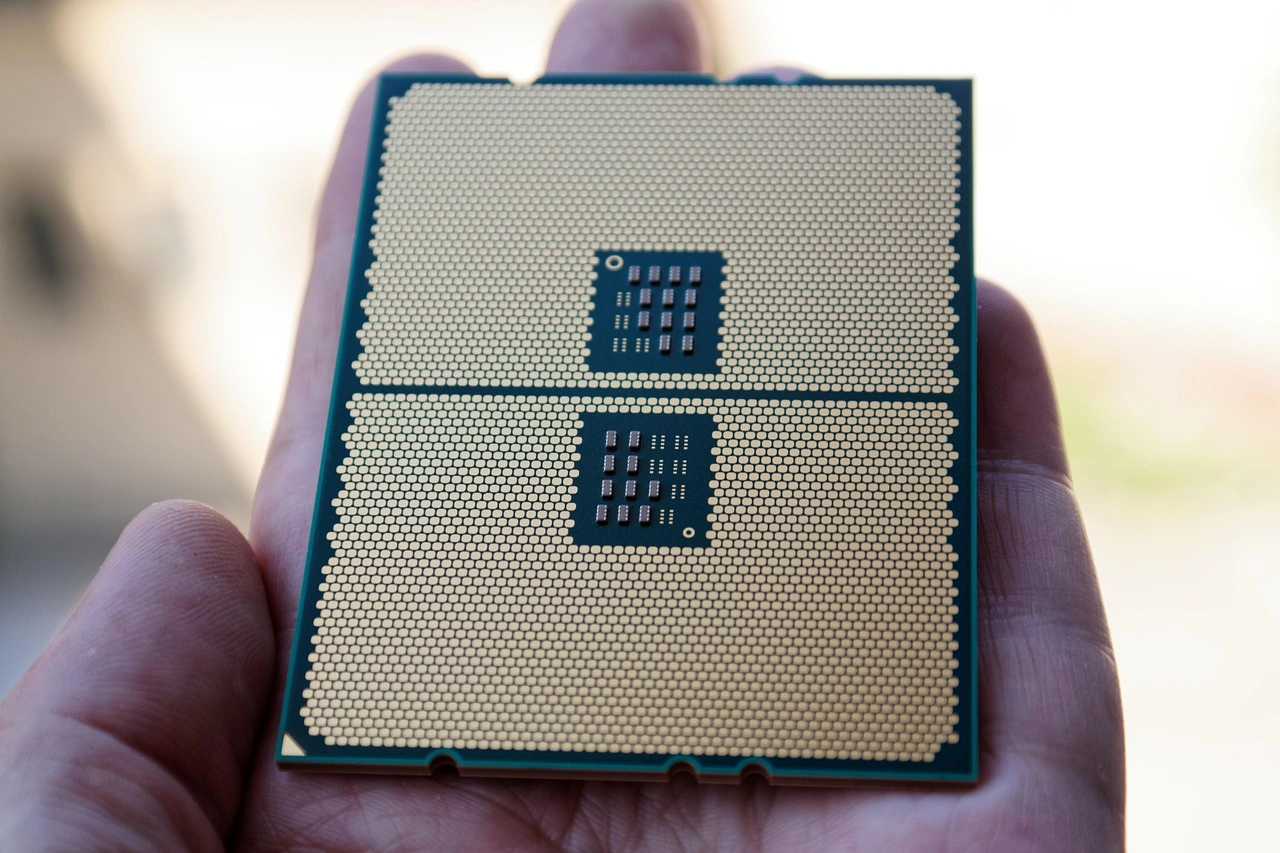
Scattered Spider cybercrime group executes sophisticated social engineering and SIM swapping attacks against enterprises, stealing millions in cryptocurrency and sensitive data through MGM Resorts and Caesars Entertainment breaches

Chinese Cyber Threats: Nezha Tool Transformed into a Weaponized Cybersecurity Threat

Hackers Leverage WordPress Vulnerabilities for Advanced ClickFix Phishing Campaigns

Two Scattered Spider cybercrime group members charged with orchestrating $115 million ransomware attacks targeting MGM Resorts and Caesars Entertainment using sophisticated social engineering and SIM swapping techniques